Security
Heata takes the security of client workloads seriously. Our appliances are deployed into domestic premises, which means we've built security into every layer — hardware, network, hypervisor, and software supply chain. We hold ourselves to a higher standard because the deployment model demands it.
Full security documentation is available under NDA. Contact security@heata.co to request it.
Isolation
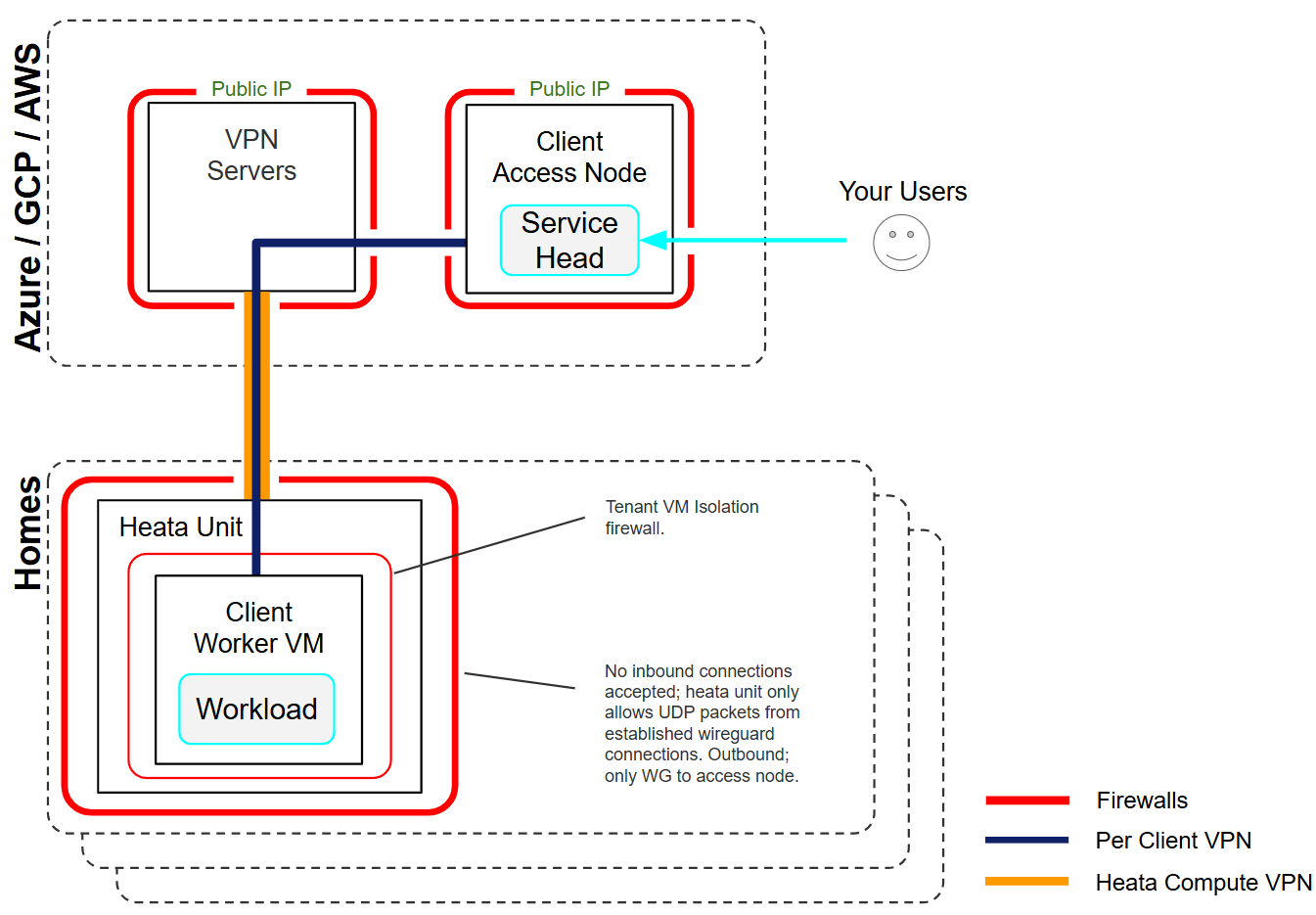
- VM isolation — all client workloads run inside dedicated KVM/QEMU virtual machines with isolated vCPU, memory, and storage. No client code executes on the bare metal host.
- Per-client WireGuard networks — each client gets a dedicated encrypted VPN. Tunnels terminate inside the client VM; the host OS cannot inspect client traffic.
- No shared storage — client VMs use dedicated virtual disk images. The host filesystem is not mounted into guest VMs.
- Tenant separation — no shared control plane or shared nodes between clients.
Encryption
- At rest — LUKS2 full-disk encryption (AES-256-XTS) on all appliances, with keys sealed to the hardware TPM
- In transit — all traffic traverses WireGuard VPN tunnels (ChaCha20-Poly1305, Curve25519). There is no administrative or data path that bypasses the VPN
- Defence in depth — client VM traffic is encrypted by a WireGuard tunnel inside the VM, layered on top of the host VPN
Hardware Security
- TPM 2.0 on every appliance — Secure Boot chain, PCR-sealed disk encryption. If the boot chain is tampered with, the TPM refuses to release the encryption key and the machine will not boot
- Chassis intrusion detection — Physically inaccessible; security tagged hardware with sensors; physical case opening triggers immediate automated response
- USB device fingerprinting — any change to connected USB devices is flagged and investigated
- BMC/IPMI hardened — IPMI disabled, per-device strong BMC passwords, PXE boot disabled
Network Security
- DENY-ALL firewall — all inbound and outbound traffic is dropped by default. Only WireGuard and DHCP are permitted
- No public IP exposure — appliances are not directly addressable from the internet
- No NAT — end-to-end addressing preserved for full auditability
- Dual-VPN admission — appliances must pass security checks on a triage network before being admitted to the production network
Automated Threat Detection
- PANIC system — real-time checks for USB changes and chassis intrusion. Failures trigger immediate VPN disconnection and operator alerting
- Lynis security auditing — 300+ security tests on every reboot, diffed against a stored baseline. Deviations block production admission
- Centralised logging — all appliance logs forwarded in real time for forensics and audit
- Continuous monitoring — Nagios-based health checks on CPU, disk, memory, temperatures, services, and VM status
Platform
- Immutable OS — SUSE Micro OS with read-only root filesystem. OS binaries cannot be modified at runtime
- Signed kernels — UEFI Secure Boot with Heata-signed kernels only. Unsigned or third-party kernels cannot boot
- Transactional updates — applied atomically with rollback capability. The system is never partially updated
- Pinned container images — SHA256 digest pinning for all infrastructure containers
Access Control
- SSH public-key only — no password-based access to any infrastructure component
- VPN-gated administration — all management interfaces accessible only over WireGuard
- Two-factor authentication — required wherever supported
- Quarterly firewall reviews — all cloud firewall rules audited on a regular cycle
Compliance
- Cyber Essentials Plus certified
- Third-party penetration testing — conducted by external security consultancy
- Physical device testing — hardware security validated independently
Full documentation
Our complete security policy is a detailed document covering platform architecture, cryptography, TPM, network security, automated monitoring, physical security, access control, software supply chain, incident response, and compliance. It is intended for enterprise security teams and is available under NDA.
- Request access: security@heata.co
Your compute on Heata provides free hot water for families around the UK.